

Privacy Policy
PH1 Research Privacy & Data Security Policy
PH1 Research takes data security and data privacy very seriously. In the course of our work, we collect, manage, and process data for our own agency and on behalf of our clients. We uphold a strict privacy and data usage policy that includes, and is not limited to, as outlined below.
Use of information:
PH1 Research collects user information for the purposes of recruiting research participants, conducting research, analyzing research, and reporting on the data that has been collected. will use each category of Personal Information listed below for purposes of conducting research, producing presentations and reports regarding the research conducted, to help our clients make informed decisions about the product or services they are developing. PH1 Research also may use Personal Information for its internal purposes to improve the quality of its products and services.
Data collected:
PH1 Research may collect one or more of the following categories of Personal Information from research participants.
Personally identifiable information (PII), such as my name and contact information. This information is collected to:
1) Facilitate prompt and robust recruitment and scheduling of research participants; or
2) Award survey participants who are selected to receive a monetary award, when this is a component of the survey in question.
Protected classifications, such as, but not necessarily, race, sex, age, national origin, disability, citizenship status, and family information.
Audio, electronic, visual, or similar information, such as images, photographs, screen-sharing, video, or recordings of participants and/or research sessions.
Education information about the level of education I have attained.
Professional or employment-related information.
Inferences drawn to create a profile reflecting my preferences or characteristics, including information about how I may use the products and services, and information relating to my general preferences or approaches to life and work.
Other information that is not otherwise listed here, but is required to complete the project
Unless otherwise requested, PH1 Research deletes all PII and participant videos 90 days after a project has been completed.
Data storage & compliance:
PH1 Research is primarily governed by the laws of British Columbia, and as such is FIPPA (Freedom of Information and Protection of Privacy Act) compliant by default. When working in other regions, we will comply with the strictest data privacy requirements of the jurisdictions in question.
In order to comply with localized data compliance laws, we use tools and storage servers that are localized to region.
General data storage:
Survey collection and storage is hosted on Qualtrics, with servers in Canada or the United States, or on Alchemer with servers in the United States
File storage is hosted on Google Drive with SOC compliance
Video interviews are conducted through Zoom, and recorded on the cloud with servers in Canada or the United States, or recorded locally on a PH1 computer if preferred
For a full list of tools that we use and their security compliance, please contact us.
Canadian compliance:
Survey collection and storage is hosted on Qualtrics, with servers in Ontario
File storage is hosted on Sync, with servers in Quebec and Ontario
Data analysis is conducted locally on a PH1 computer, and backed up on Sync
Agency details:
PH1 Research provides employee and contractor access privileges to technology (including software, data files, networks, systems, applications, computers and mobile devices) based on the following principles:
Need to know – users or resources will be granted access to systems that are necessary to fulfill their roles and responsibilities.
Least privilege – users or resources will be provided with the minimum privileges necessary to fulfill their roles and responsibilities.
We maintain and review on an annual basis, the following policy documentation:
Acceptable Use Policy
Data Classification Policy
Data Security Policy
Access Control Policy
Security Incident Response Plan
View More Resources

A comprehensive trend analysis of feline blade fascination in the digital pet ecosystem
The Sharp Truth: Why Digital Cats Are Obsessed with Virtual Knives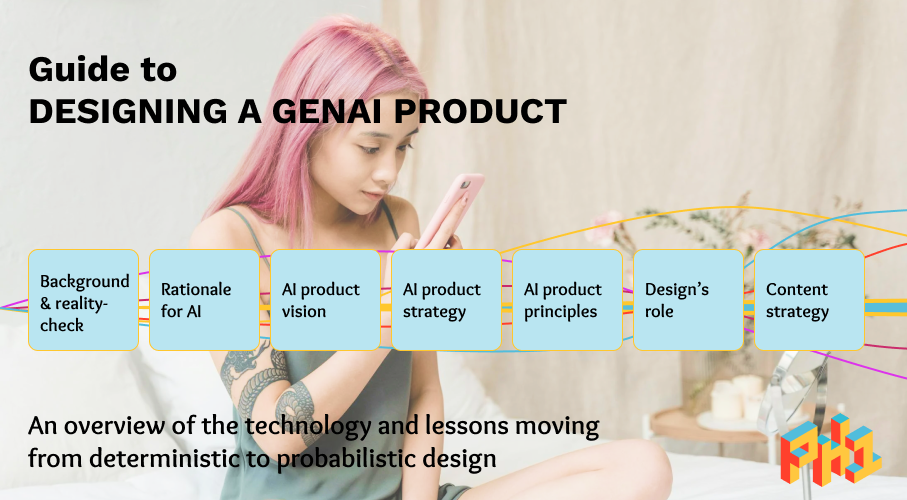
Strategy, AI, Design, Product
Guide to designing a GenAI product: From vision to content strategy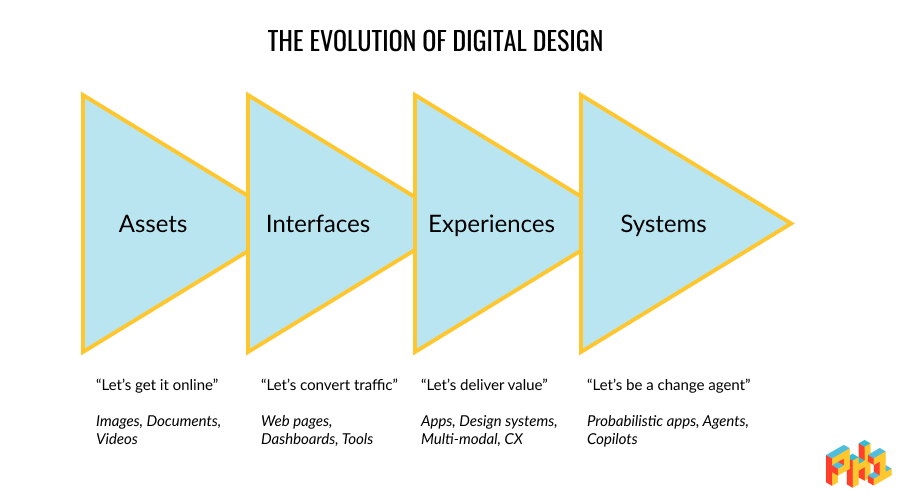
Strategy, AI, Design, Product
The end of UX? This is the start of the service design of AI
Strategy, AI, Design, Product
Build AI products that customers want | Design of AI podcast
Strategy, Methodology, Service Design
PH1 Research's Service Transformation Methodology
Strategy, Travel, Lessons
10 business lessons we learned travelling around the world
Trends, Strategy, Design
2016 Design trends: Do not fear the competition, no matter how big they are.
Trends, Innovation
Win Audiences in 2016: 6 Strategic Tips for Entrepreneurs and Business Leaders
Strategy, Gamification, Marketing
Guide to gamification: strategies to increase engagement and make your audience feel special
Tips
4 ways we helped entrepreneurs and business leaders around the world
Innovation, Strategy, Disruption
The disruption no one is talking about
Innovation, Assessment
Your business model will be disrupted if this describes your organization
AI, Innovation, Design Thinking
The key to solving problems and designing solutions that an AI can’t: Irrational behaviour
Innovation, Future-proofing
Thanks to Google, the end of the mobile app is near
Innovation, Engagement, Future
Forget VR — Mobile cameras are the greatest innovation your business must embrace
Travel, Tourism, Trends
Asia-Pacific travellers: about to transform the global tourism industry
Article, Innovation, Competition
It’s time to realize you’re already competing with Amazon, Google, Facebook, Apple
Not only is health care challenged by aging, so is the way of life of rural citizens
Japan and North America's Aging Problem that startups must address
CX, UX, Research
Innovating your organization begins by understanding your customer experience
CX, UX, Research
Becoming customer-centric: What most organizations get wrong
Research, Public Health, Strategy
Our personal views about health are changing the way we want to be engaged
CX, Toolkits
Becoming customer-centric: 3 toolkits to measure your Customer Experience
COVID-19, Resources, Research
PH1's research initiative to improve the CX of organisations impacted by COVID-19
BlackLivesMatter, Accessibility
Researchers can help end systemic racism that plagues products and services
Research, COVID-19, Lessons
3 lessons: Becoming an adaptive & resilient organization
Public health guide
Information Architecture for Public Health Organizations
Tips & lessons
Strategies for success: Usability testing & user research of government websites and public services
Tips & lessons
Recruit the right audience for your research: Social media recruitment
Methodology and Examples
Intro to Customer Experience
Tips & lessons
How to create customer journey maps & journey mapping tips
Outcome of our annual planning retreat
PH1 Research's 2022 Strategic Vision
Privacy Policy
PH1 Research Privacy & Data Security Policy
Methodology and Examples
Intro to Service Design
Methodology and Examples
Intro to Innovation Sprints
UX, strategy, human-centred design
UX needs to set the bar higher than usability
Innovation methodology
Turning Fandom into Revenue with Web3
About Us
Our Epic Annual Remote Retreat: Colombia Edition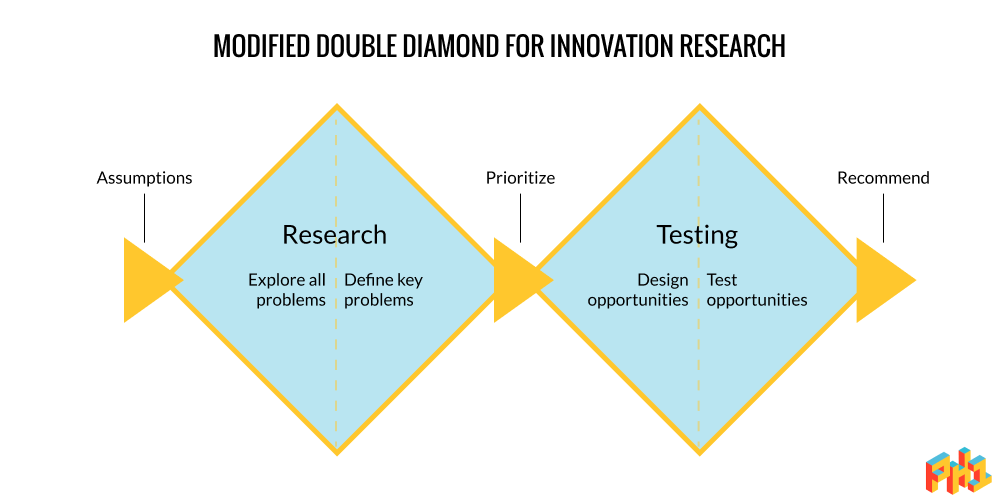
Innovation research guide
Guide to researching new products & testing concepts
Innovation methodology
A guide to overcoming uncertainty impacting your product or service
Innovation methodology
For More Impactful UX Strategy, Use Futures Thinking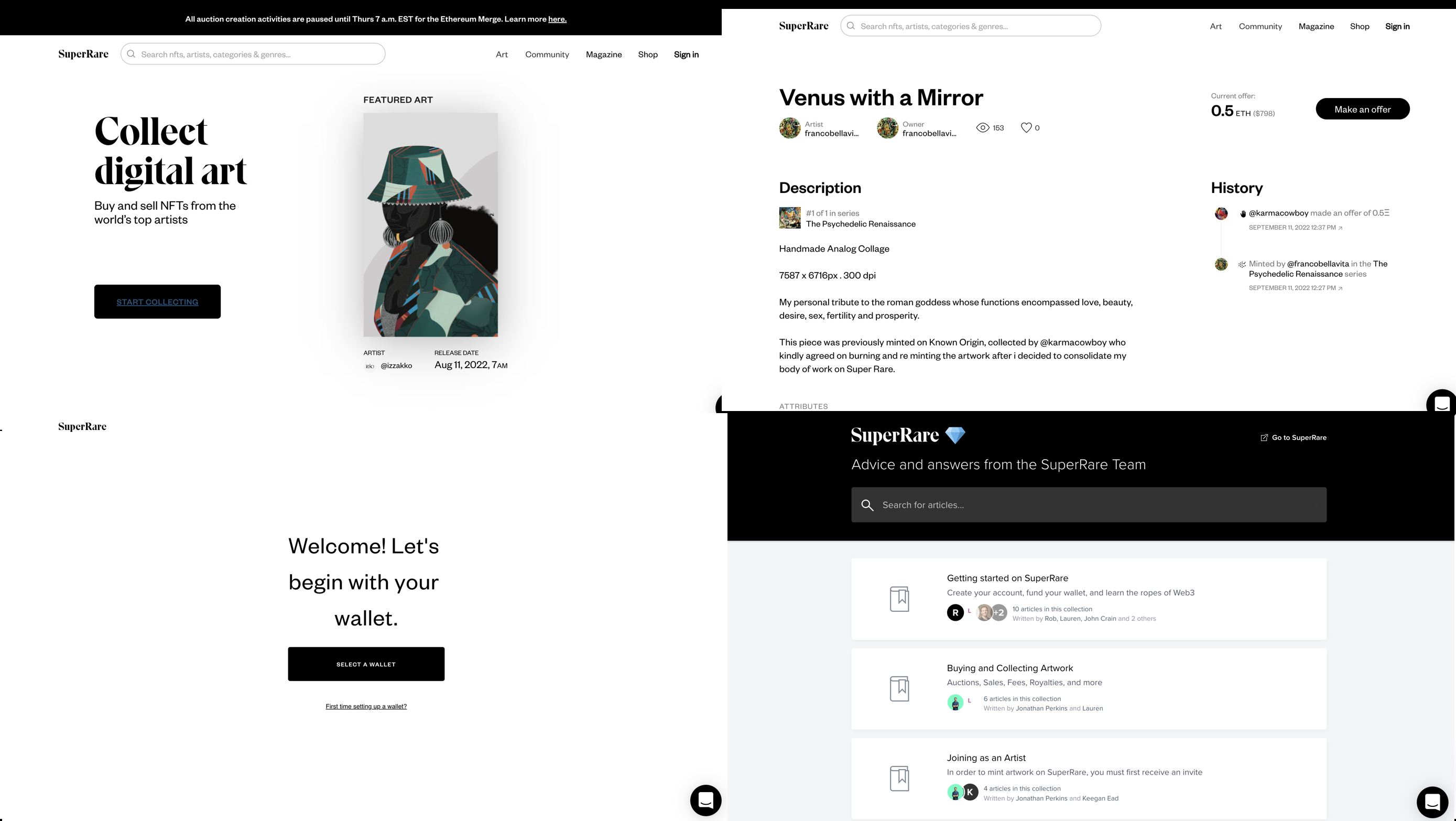
Audit & analysis
Web3 has a major UX problem
Tips & lessons
10 lessons about how to improve tech & your success as a researcher, designer, product manager
 Our Work
Our Work